Creating a Holistic Ransomware Response
OnDemand TechTalk
Discover the best practices for protecting and recovering not only your data from a ransomware attack but your entire data center.
In this educational TechTalk, our world-class speakers provided thought leadership on the latest strategies and best practices for protecting your valuable data from ransomware attacks. We delved into the intricacies of ransomware threats and equipped you with the knowledge and tools to improve your organization's defenses and response strategy.
Register for the TechTalk
We also demonstrated the encryption of a Windows virtual machine, showcasing our advanced detection technology and promptly alerting the administrator. Furthermore, we highlighted the speed at which they could recover from the attack, providing a practical demonstration of our efficient recovery process.



Featured Speakers
Yan Ness: CEO, VergeIO: Before joining VergeIO, Ness was CEO of Online Tech, the Midwest's Leading Secure, Compliant Enterprise Hosting Company with 7 Data Centers across Michigan and Indiana. His team at Online Tech had to prepare and respond to cyber threats every day.
Jeff Campbell: Runs VergeIO's Customer Success team and has first-hand experience helping customers recover from disasters and ransomware attacks.
George Crump: before joining VergeIO, was an IT Analyst for 15 years and spent five years leading TechTarget's SearchStorage and SearchDisasterRecovery workshops, training IT professionals worldwide to develop fully functioning disaster recovery plans.
Agenda
Building a Solid Defense Foundation
- Learn about the vulnerabilities of Virtual Machines (VMs), hypervisors, metadata, backup software, and even network switches.
- Discover the importance of a hardened operating environment in reducing ransomware threats and vulnerabilities.
Unparalleled Data Resilience
- Explore the concept of unlimited and unchangeable clones and their role in preserving data integrity.
- Understand the advantages of clones over snapshots as it pertains to ransomware defense and recovery.
Proactive Detection and Alerting
- Learn the importance of rapidly detecting ransomware anomalies and empowering you to limit the damage, identify the most appropriate recovery method and take swift action.
- Learn how to create ransomware honeypots to understand how to improve your resiliency.
Rapid Recovery for Business Continuity
- Discover how IOfortify enables speedy restoration of systems, virtual machines, and even entire data centers, minimizing downtime and ensuring business continuity.
- Learn how to recover quickly while maintaining forensic capabilities to understand the "how" of the attack.
Real-life Success Stories
- Hear from VergeIO customers who have successfully restored their systems to a secure state within minutes.
- Gain valuable insights from testimonials and case studies, showcasing the effectiveness of IOfortify in real-world scenarios.
IOfortify Product Demonstration
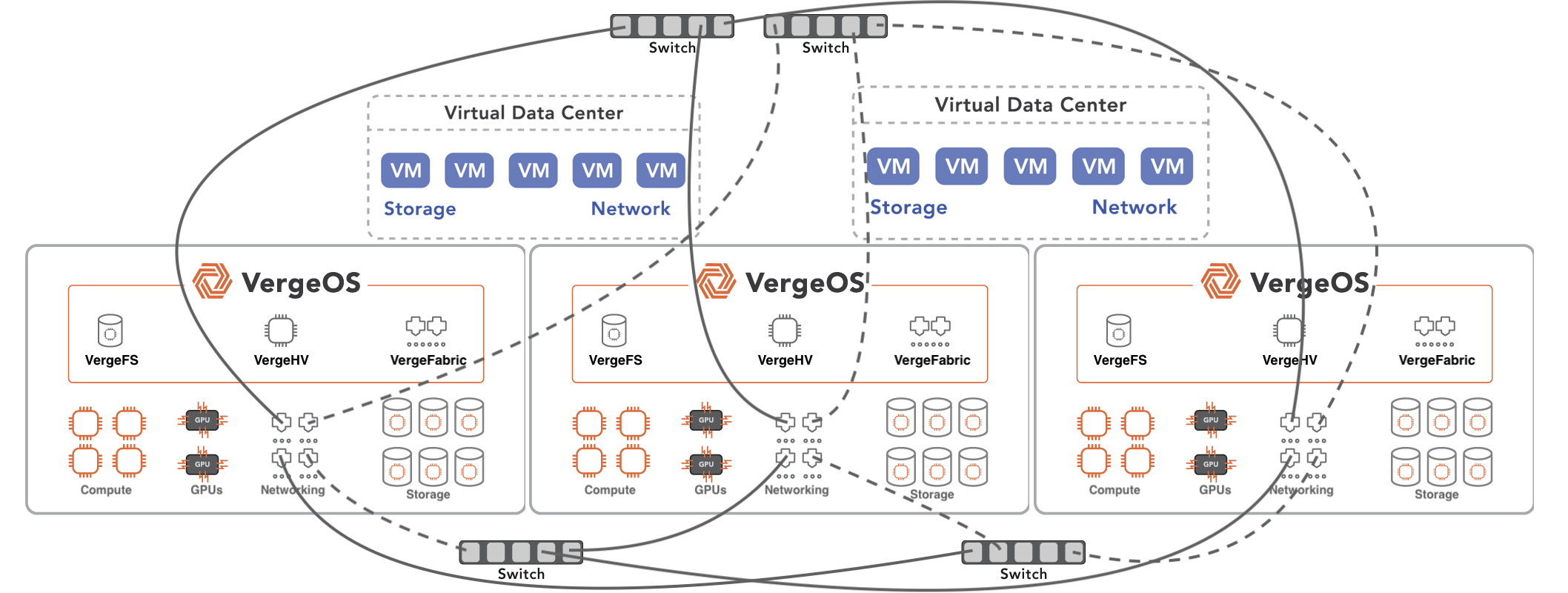
- Understand the foundation of IOfortify, the ultimate solution for Holistic ransomware protection and recovery.
- Explore the integration of IOfortify into VergeOS and its key features.
- See IOfortify in action
Don't miss this opportunity to gain insights from industry leaders and stay ahead of the constantly evolving ransomware landscape. Register now to secure your spot!
About VergeIO
VergeIO is a leading provider of unltraconverged infrastructure solutions, committed to empowering organizations with robust and reliable technologies. With IOfortify, we redefine ransomware protection by combining state-of-the-art security measures, unlimited clones, and rapid recovery capabilities. Our mission is to equip businesses with the tools and knowledge to fortify their data integrity and ensure peace of mind.