VMware alternative DR sounds straightforward on paper. You replace the hypervisor, migrate the workloads, and the backup infrastructure follows. In practice, the backup question is the one that stops organizations cold. Modern ransomware encrypts 400 VMs at 2 a.m. on a Tuesday, and the distance between a documented recovery plan and a working recovery becomes painfully clear within the first 60 minutes. For organizations in the middle of a VMware exit, that crisis arrives while everything is still in motion.
 The organizations now leaving VMware face a compounding version of this problem. They are replacing their hypervisor, re-architecting their storage, and migrating workloads to new infrastructure. During that transition, the backup and recovery layer has to keep working. Not after the migration finishes. Not once the new platform stabilizes. Right now, while everything is in motion.
The organizations now leaving VMware face a compounding version of this problem. They are replacing their hypervisor, re-architecting their storage, and migrating workloads to new infrastructure. During that transition, the backup and recovery layer has to keep working. Not after the migration finishes. Not once the new platform stabilizes. Right now, while everything is in motion.
VergeOS’s support of the oVirt API changes the math on VMware alternative DR by splitting the recovery job into two specialized layers. VergeOS handles the first 60 seconds to 60 minutes of a crisis with instant rollback, immutable snapshots, and tenant isolation. Veeam handles the next 60 days with historical recovery, compliance pulls, off-platform restores, and air-gapped copies. The two-layer model is not redundancy. It is specialization, and it delivers a recovery posture that most VMware environments never had.
Key Takeaways
The First 60 Seconds: Platform-Level Disaster Recovery with VergeOS
A ransomware attack moves fast. Modern strains encrypt data at rates that can flatten a midsize environment in minutes. The first question in any incident is not “how do we restore?” It is “how do we stop the bleeding?” VergeOS answers that question at the platform level.
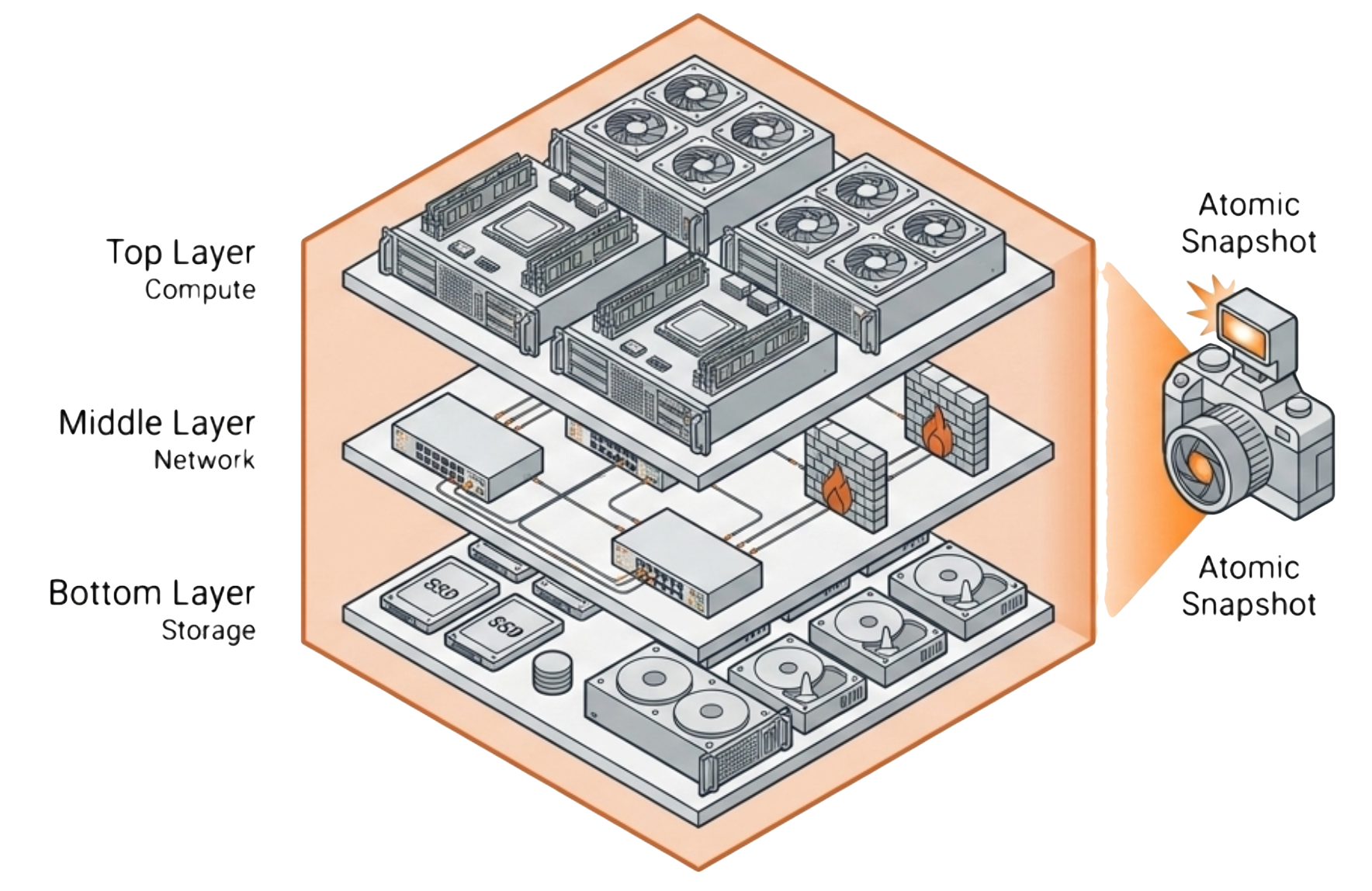
Immutable snapshots add a second layer of defense. VergeOS snapshots cannot be modified or deleted by any process running inside the virtual environment, including a compromised administrator account. Ransomware that gains root access to a VM still cannot touch the snapshot layer. This architectural separation between the workload and the protection mechanism is what makes platform-level immutability different from application-level backup encryption. Tenant isolation closes the third gap: if ransomware compromises one tenant, the blast radius stops at that tenant boundary. Other workloads continue running on the same cluster without exposure.
Key Terms
In VergeOS, a complete software-defined environment that encapsulates compute, storage, networking, and security policy as a single object. A VDC snapshot captures the full state of that object atomically.
A point-in-time copy that cannot be modified or deleted by any process running within the protected environment, including compromised administrator accounts. VergeOS implements immutability at the architecture layer, not the application layer.
VergeOS runs multiple virtual data centers on shared physical hardware with full network and storage separation between them. Isolation means a security incident in one tenant cannot spread to adjacent tenants on the same cluster.
The standard REST API for KVM-based virtualization management. VergeOS 26.1.2 implements oVirt-compatible endpoints, allowing backup tools that support oVirt — including Veeam — to connect without custom development.
A Veeam capability that understands the internal structure of applications like Exchange, SQL Server, and Active Directory. Enables granular restores of individual mailboxes, database tables, and AD objects from a single backup job.
The Next 60 Days: Granular Backup Recovery with Veeam
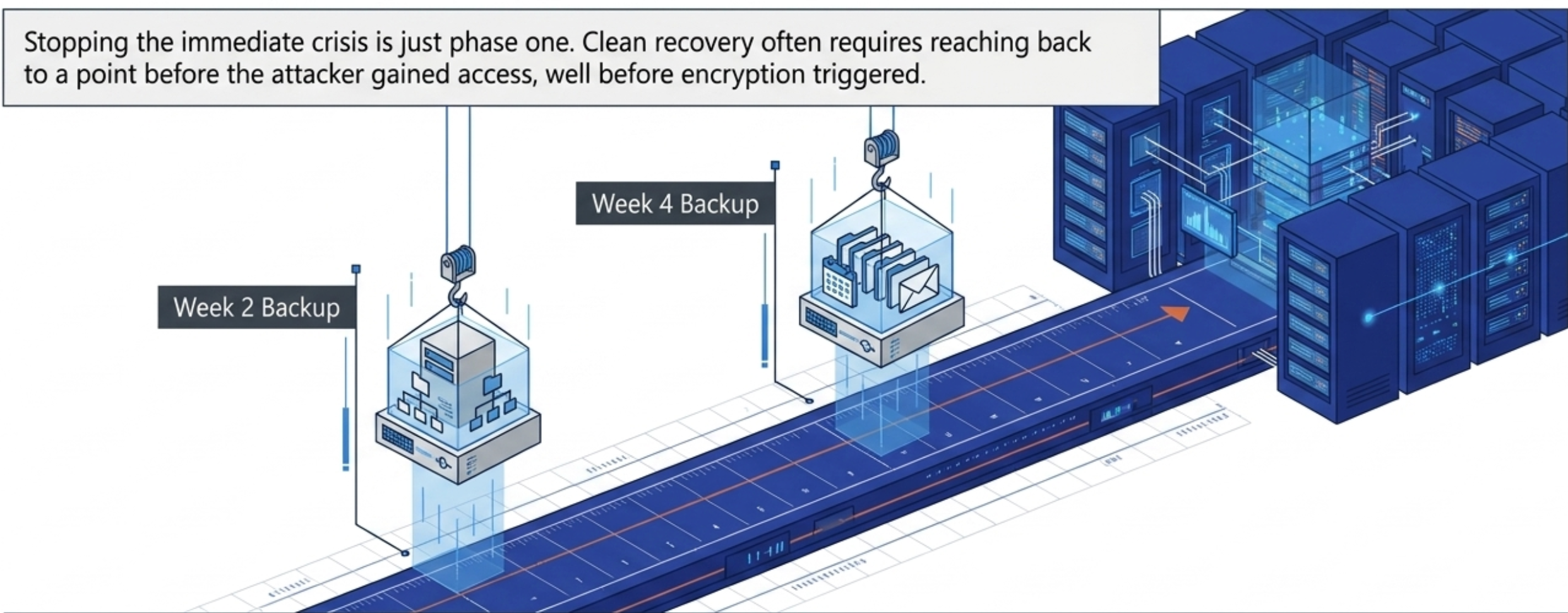
Historical recovery is the first requirement. Veeam maintains backup chains that stretch back weeks, months, or years depending on the retention policy. After a ransomware event, forensic teams often discover that the initial compromise happened days or weeks before the encryption triggered. Clean recovery requires reaching back to a point before the attacker gained access, not just before the encryption started. Veeam’s granular recovery points make that reach-back possible at the individual VM, application, or file level. Compliance pulls represent the second requirement: Veeam’s application-aware backups understand the internal structure of Exchange, SQL Server, Active Directory, and Oracle workloads, making it routine to pull a single mailbox from a three-week-old backup or restore a specific database table to a point in time.
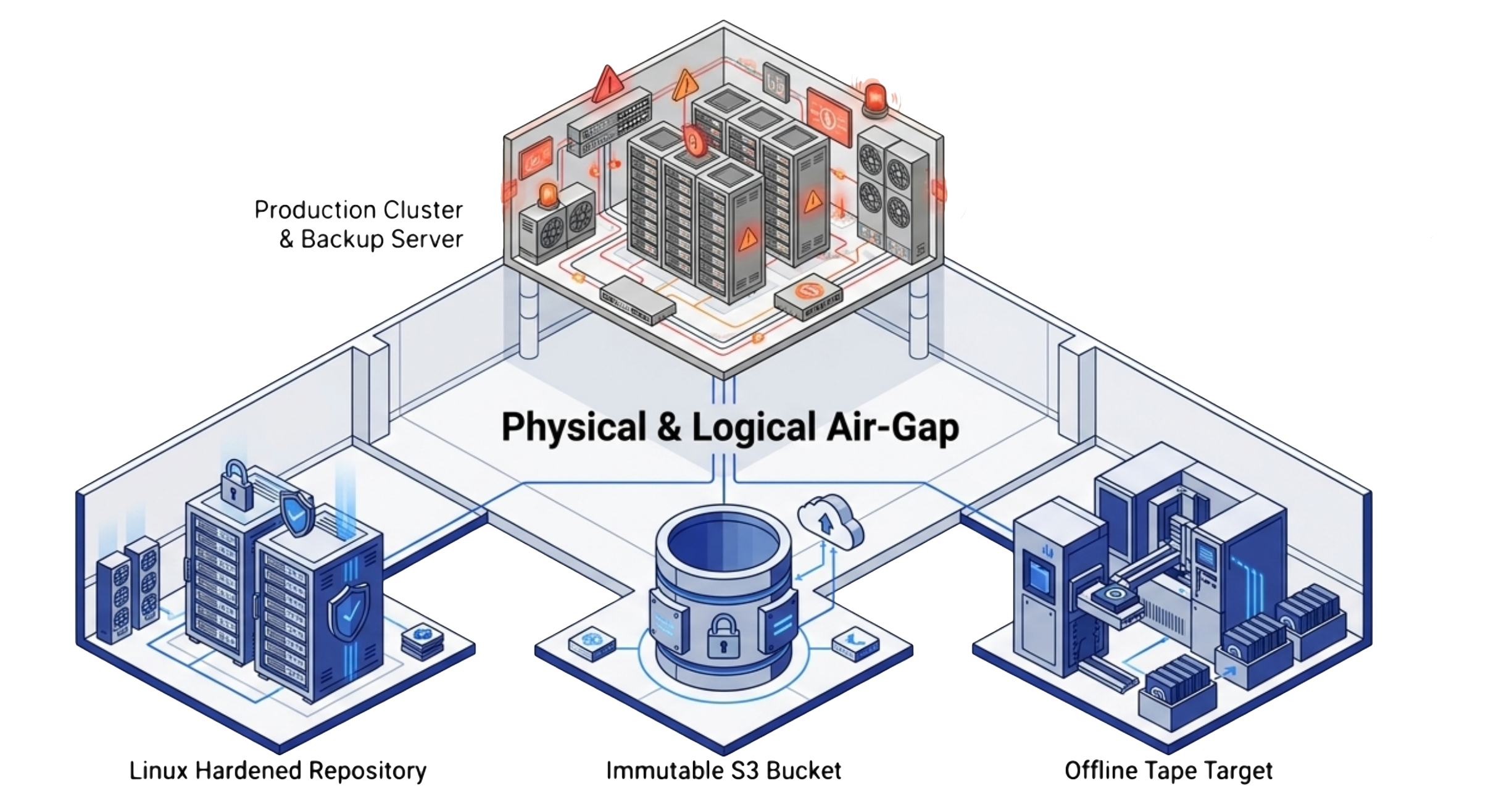
Off-platform restores address the third requirement. A serious disaster sometimes destroys or compromises the primary infrastructure entirely. Veeam restores to physical hardware, alternative hypervisors, and all major cloud platforms — portability that means the backup is never locked to a single infrastructure vendor. Air-gapped copies close the fourth requirement. Veeam supports immutable backup repositories, Linux hardened repositories, and tape targets that create a physical separation between production data and backup data. Ransomware that compromises both the hypervisor and the backup server still cannot reach a copy stored on an air-gapped tape library or an immutable S3 bucket.
Why Two Layers Beat One: VergeOS and Veeam vs. VMware’s Single-Layer Model
The traditional VMware model placed enormous weight on the backup layer alone. VMware’s native snapshot capabilities carried well-documented performance penalties, and vSphere had no concept of a virtual data center snapshot that captured compute, networking, and storage together. The backup product handled everything from operational recovery to long-term retention to compliance. That single-layer model created a fragile recovery posture. If the backup failed, recovery failed. If the backup server was compromised, retention was compromised. If the backup took four hours to restore a critical application, the business waited four hours regardless of the severity of the outage.
The VergeOS and Veeam model splits the recovery job along a natural boundary. VergeOS owns the fast, platform-level response: snapshots are instant, rollbacks affect entire environments, and immutability is architectural, not bolted on. Veeam owns the deep, long-duration recovery: retention stretches for years, granularity reaches individual files and application objects, and portability extends across platforms and clouds. This split is not a workaround or a transitional architecture. It is a fundamentally better approach to VMware alternative DR. The platform layer handles what platforms handle best, and the backup layer handles what backup handles best — with no overlap or conflict between them.
The oVirt Migration Path: Preserving Veeam During a VMware Exit
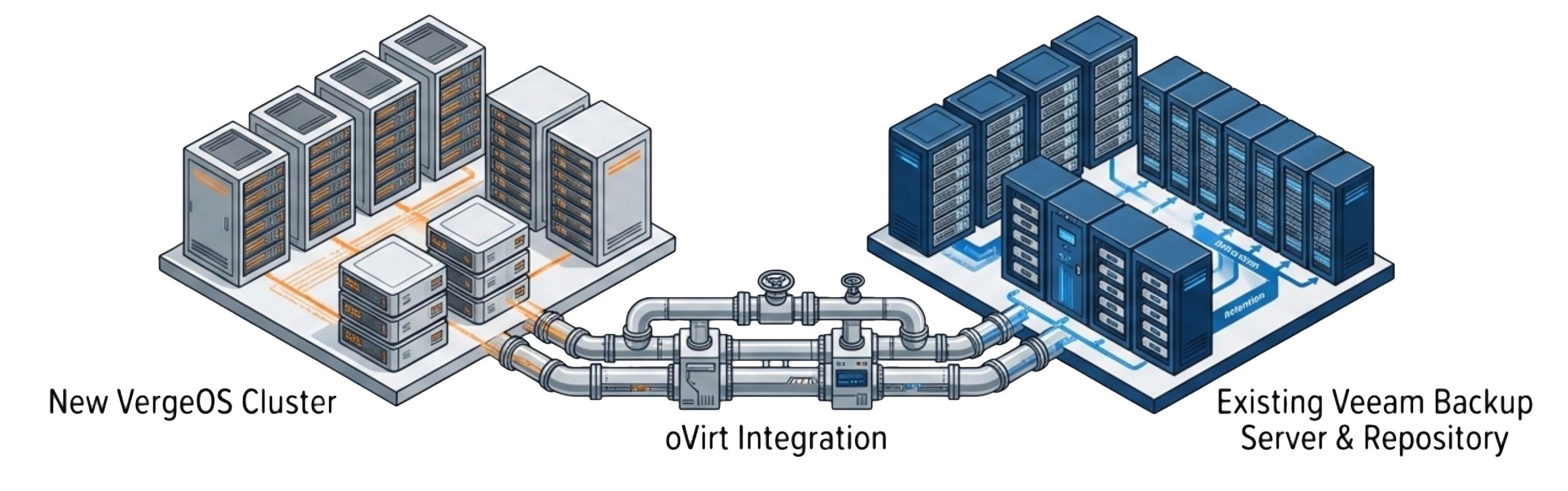
Veeam treats VergeOS as a first-class hypervisor target through the oVirt driver, and all existing Veeam licenses and contracts remain valid. This continuity matters during a transition that already involves significant operational change. Replacing a hypervisor is a project. Replacing a hypervisor and a backup platform at the same time doubles the risk and the workload. VergeOS’s Veeam support via oVirt eliminates that double migration by keeping the backup layer stable while the compute layer modernizes.
The migration path is straightforward. Add VergeOS as an oVirt KVM Manager in the Veeam console, point it at the VergeOS API endpoint, and Veeam discovers the workloads through the standard oVirt inventory. Existing protection policies apply to discovered workloads immediately. The entire connection takes under an hour in a production-style environment — as Rick Vanover and Paul Hodges demonstrated in the live demo recorded April 16, 2026.
A Real Scenario: Ransomware at 2 a.m.
Consider a 500-VM environment running VergeOS with Veeam backup. Ransomware triggers at 2 a.m. and begins encrypting workloads across two production tenants. The on-call engineer receives an alert within minutes using VergeOS alerting. They use the VergeOS console to identify the affected tenants and roll back both virtual data centers to snapshots taken 15 minutes before the encryption started. Production workloads are running again on clean snapshots within 10 minutes of the rollback command. The unaffected tenants on the same cluster never went offline.
Over the next 48 hours, the security team determines that the attacker gained initial access 11 days before the encryption event. Veeam’s backup chain provides recovery points going back 30 days. The team restores specific file server data and database instances from the 12-day-old backup to extract clean copies of data the attacker accessed before triggering encryption. Veeam’s application-aware restore pulls individual Active Directory objects and Exchange mailboxes for the forensic investigation. Three weeks later, the compliance team needs to produce email records from the compromised period for their insurance carrier. Veeam pulls those records directly from the granular backup without restoring an entire Exchange server. No single product handles all three phases. VergeOS handled the first phase in minutes. Veeam handled the second and third phases over weeks.
Rick Vanover (Veeam) and Paul Hodges (VergeIO Field CTO) walk through a complete deployment — from blank environment to full Veeam coverage on VergeOS in a single session. Live demo and full Q&A included.
Watch On-Demand →The session goes beyond slides. It walks through the Veeam console adding VergeOS as an oVirt KVM Manager, running the first backup job, and restoring a workload — end to end.
The Q&A addresses the questions most teams ask during a VMware exit: license portability, retention policies during migration, and how the two-layer model changes the RPO and RTO conversation with the business.
VMware-Only DR vs. VergeOS + Veeam Two-Layer DR
| VMware + Backup Only | VergeOS + Veeam | |
|---|---|---|
| Platform-level recovery | Individual VM restores only | Entire VDC rollback in seconds |
| Immutability | Backup product layer only | Architectural — built into VergeOS platform |
| Blast radius containment | None at hypervisor level | Tenant isolation stops spread at VDC boundary |
| Time to operational recovery | Hours to days | Minutes for platform recovery; Veeam handles granular in parallel |
| Backup tool compatibility | VMware vSphere API only | Veeam via oVirt driver — existing licenses valid |
| Long-term retention | Backup product | Veeam — weeks, months, years with granular recovery points |
| Compliance pulls | Via backup product | Veeam application-aware — file, mailbox, database level |
| Air-gapped copies | Via backup product | Veeam Linux hardened repo, immutable S3, or tape |
Ready to see VergeOS in action? Take a Test Drive Today.


